Kristin King,
CEO, AnzenOT & AnzenSage
VP - Food Cybersecurity
Cybersecurity Association of the Food Industry
>profile
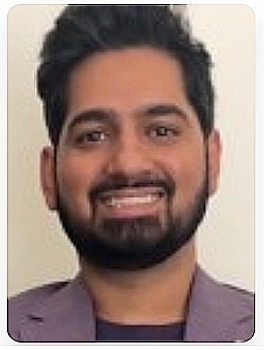
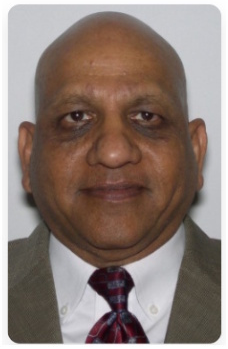
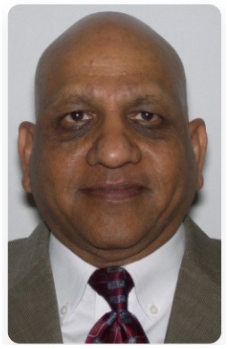
Juan F. Villarreal
Principal, Energy Infrastructure Resilience & Industrial Cybersecurity
Villarreal Energy LLC
>profile
Day 3 of the Symposium focuses on one of the most urgent and rapidly evolving challenges facing the electric sector: the influence of AI and machine learning agents on industrial control system cybersecurity. This interactive workshop is designed for OT security practitioners and critical infrastructure operators who are ready to move beyond theory and examine the documented realities of AI-enabled cyber threats.
Drawing on recent research and real-world incidents, the program will explore how AI can accelerate reconnaissance, vulnerability discovery, and coordinated attacks across IT/OT environments, while also examining the governance, authentication, and operational guardrails required for responsible deployment of AI within critical energy systems. Structured around both the offensive and defensive dimensions of AI in ICS environments, the day emphasizes practical engagement, technical depth, and open discussion of the unresolved challenges utilities and operators must address now.
Workshop Facilitators
Get in touch
Copyright 2026 Smart Grid Observer. All rights reserved